Your external infrastructure is one of your most commonly targeted attack surfaces. Perform an external infrastructure penetration test to identify vulnerabilities and ensure that your perimeter is fortified against attackers who may attempt to gain deeper access into your organisation.
External Infrastructure penetration testing
External Infrastructure penetration testing with OnSecurity
OnSecurity highlights weaknesses within your organisation’s external infrastructure. By proactively addressing potential weaknesses, you can significantly reduce the risk of unauthorised access and safeguard critical systems and data from cyber threats.
Gain insight into your vulnerabilities
You'll be able to understand where your external network is most vulnerable, see how attackers could exploit these vulnerabilities snd receive clear, practical guidance to address and fix identified security issues.
Enhance perimeter defence
Ensure you only make sure only authorised users can access critical systems, improve the security of the network services and configurations and block unauthorised attempts to gain access to the network.
Safeguard sensitive data
You'll be able to identify weaknesses that could lead to data breaches, verify your encryption methods protect data in transit and eliminate vulnerabilities that could be exploited by attackers.
What is network penetration testing?
External network penetration testing involves ethical hacking of your organisation’s internet-facing systems and networks. External systems can include web applications, networks, FTP servers, mail, routers, login systems, and sub-domains. This process simulates the techniques used by real-world attackers to test your defences, identify vulnerabilities, and evaluate your security posture. The key objectives include being able to:
- Discover unpatched systems where outdated software could be exploited.
- Assess insecure configurations that could leave your network exposed.
- Attempt to breach systems by simulating an attack and evaluating of how well your defences hold up.
- Investigate if there are secure authentication mechanisms in place and secure passwords.
- Explore any potential software flaws and ineffective firewall rules.
- Data exfiltration testing and weak encryption protocol testing to see if sensitive data could be extracted by attackers.
- Internal network access attempts by simulating efforts to breach the internal network from the outside. Replicates the techniques real-life attackers use when targeting an organisation.
Get an Instant External Infrastructure Pentest Quote
Want to know how much an external infrastructure pentest would cost? Try out our instant quote generator to get started.
Why do you need an external network infrastructure pentest?
External network infrastructure is a primary entry point for cybercriminals. Regular pentesting helps identify vulnerabilities like missing patches, weak firewall rules, and misconfigured software before attackers can exploit them. By simulating real-world threats, you can prevent data breaches, service disruptions, and reputational damage, while also demonstrating a commitment to security and compliance with industry regulations. The knowledge of your network's vulnerabilities puts you in a great place to develop your security measures and better protect yourself against attackers.

Crest-accredited external infrastructure pentesting
At OnSecurity, we deliver top-tier penetration testing services, validated by our CREST (Council of Registered Ethical Security Testers) accreditation. This ensures our methodologies, processes, and procedures meet the highest standards in the industry.
Why trust OnSecurity for your external infrastructure pentesting?
- CREST-accredited: Our practices are externally vetted, guaranteeing top-quality testing,
- Certified experts: Most of our testers are CREST-certified, proven in rigorous assessments.
- Manual-first approach: We focus on hands-on testing to catch vulnerabilities automated tools might miss.
Choose OnSecurity for expert-driven, reliable external network security.
External infrastructure security challenges
Securing your external infrastructure presents unique challenges that require specialised knowledge and proactive measures:
Exposure to cyber attacks
Internet-facing systems are constantly targeted by attackers probing for weaknesses.
Complex attack vectors
Sophisticated attackers can exploit a combination of vulnerabilities across different systems.
Evolving threat landscape
The tactics used by cybercriminals are constantly evolving, requiring regular assessments to keep defences up-to-date.
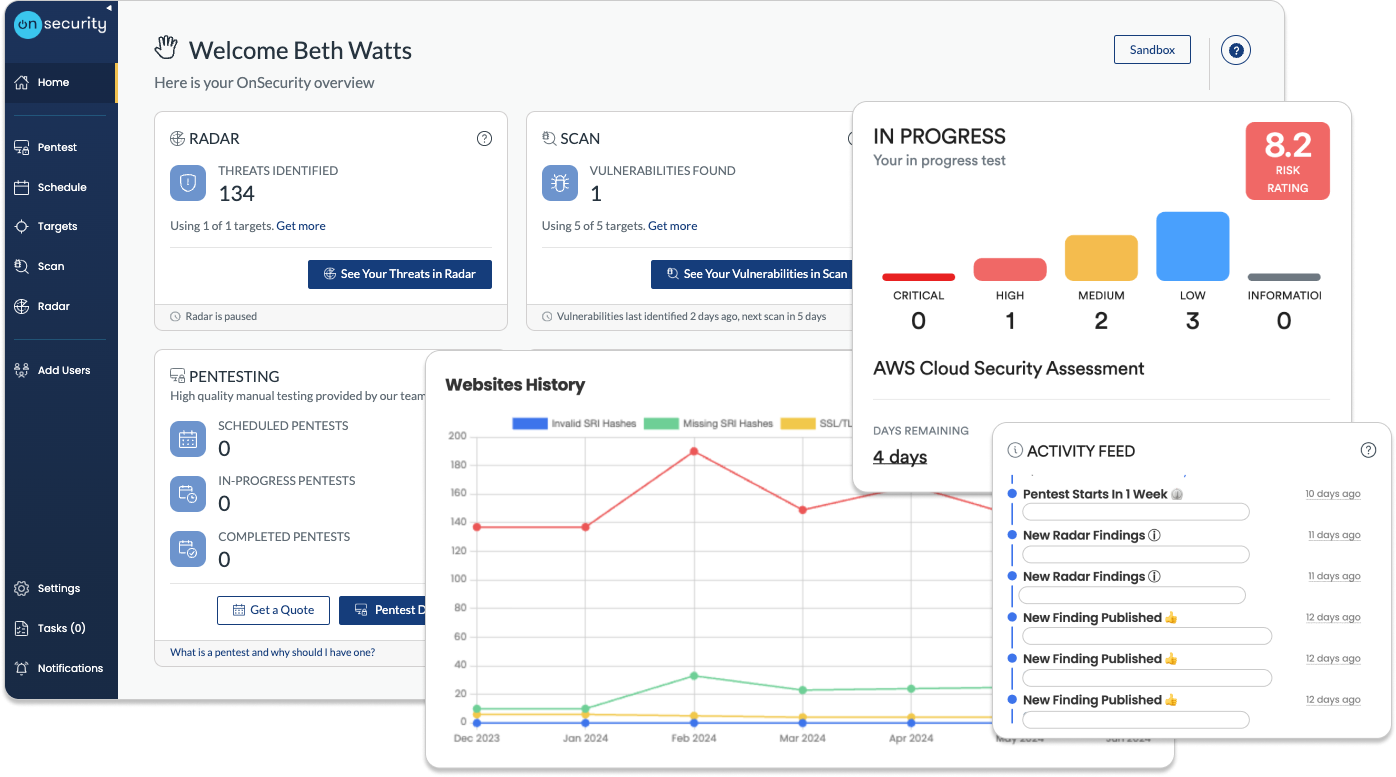
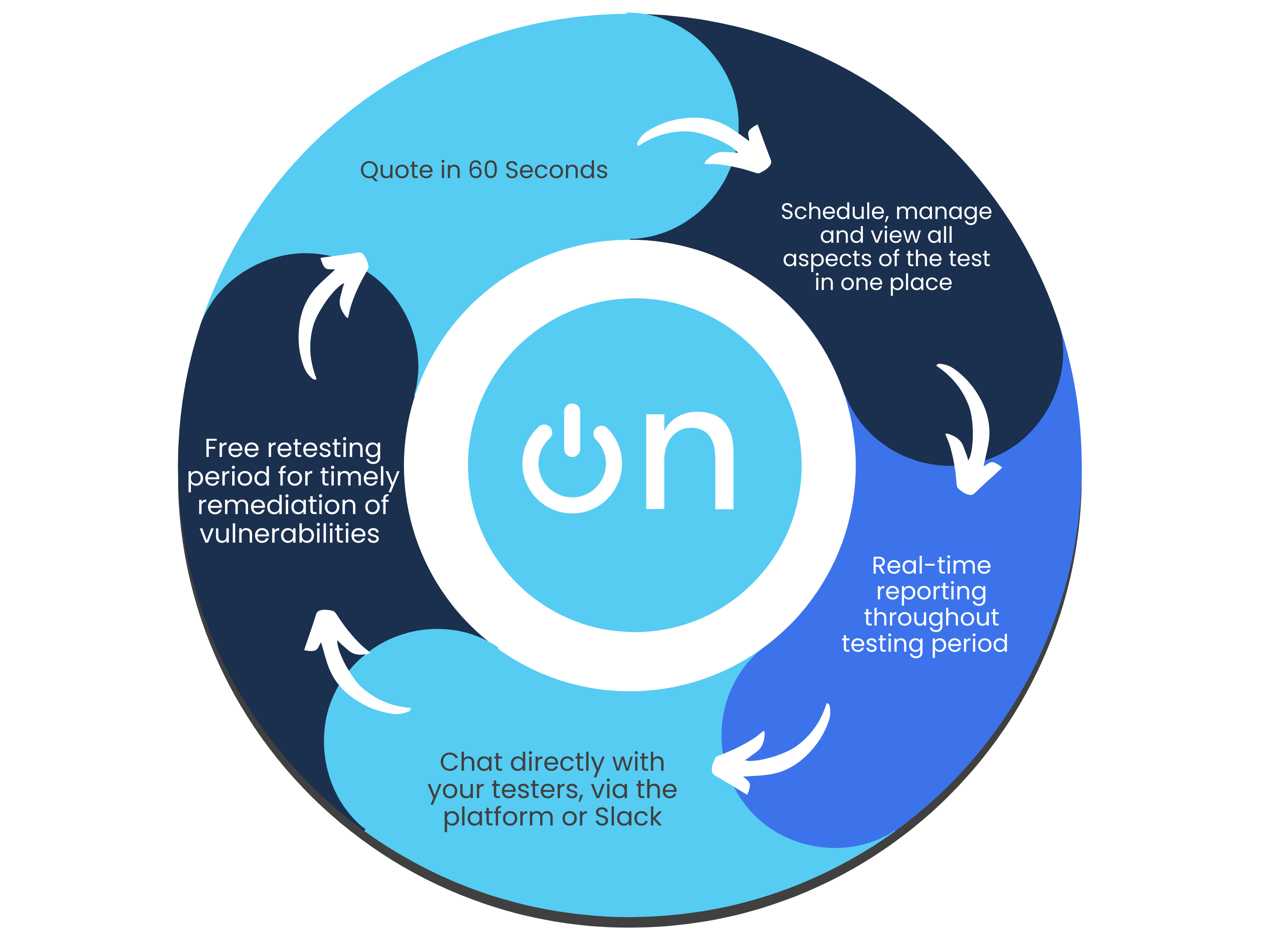
Quick, high-quality pentests
Discover why our user-friendly platform and AI + human approach make pentesting hassle- free.
Flexible subscription plans
Simplify your testing and monitoring with a single monthly payment, combining regular penetration tests and continuous vulnerability scanning. Get predictable costs while receiving ongoing protection.Instant quote & customised plans
Receive a real-time, personalised cost estimate through our intuitive platform. Tailor your testing needs with configurable options that suit your business goals and security requirements.Effortless platform access
No more long scoping processes. Book tests directly through our platform or get personalised assistance from our sales team. Enjoy streamlined communication and automated workflow notifications for maximum efficiency.Continuous, real-time testing
Stay informed with real-time progress notifications and direct communication with testers via in-platform comments. Benefit from ongoing vulnerability assessments to proactively detect and address risks.Immediate, actionable reports
Access your findings instantly through our platform. Generate detailed reports at any time, offering both technical insights and high-level summaries—without the wait.Free retests for resolved issues
Once you’ve addressed vulnerabilities, we’ll retest them for free within a flexible window, ensuring your systems remain secure at no additional cost.Ongoing protection & threat intelligence
Sign up for continuous monitoring to access automated vulnerability scanning, along with situational awareness through threat intelligence, ensuring your defences stay up to date year-round.
Other types of penetration testing
Find the penetration test to best suit your business and cybersecurity needs.
Frequently Asked Questions
What is the difference between external and internal pen testing?
External pen testing focuses on your organisation’s internet-facing systems, while internal pen testing assesses the security of your internal network and systems, identifying vulnerabilities that could be exploited by insiders or through a compromised external network.
Should the tester’s IP address be whitelisted on your system?
This really depends on the objectives of the test. In a real-world scenario, attackers have unlimited time to bypass the intrusion prevention system (IPS), and once they do, they target the same vulnerabilities a tester would identify in an external penetration test.
If your goal is to assess the effectiveness of your IPS or broader defences, whitelisting isn’t recommended. However, if you’re more interested in discovering which vulnerabilities could be exploited once an attacker bypasses detection, a time-limited test with the tester's IP address whitelisted can provide more value.
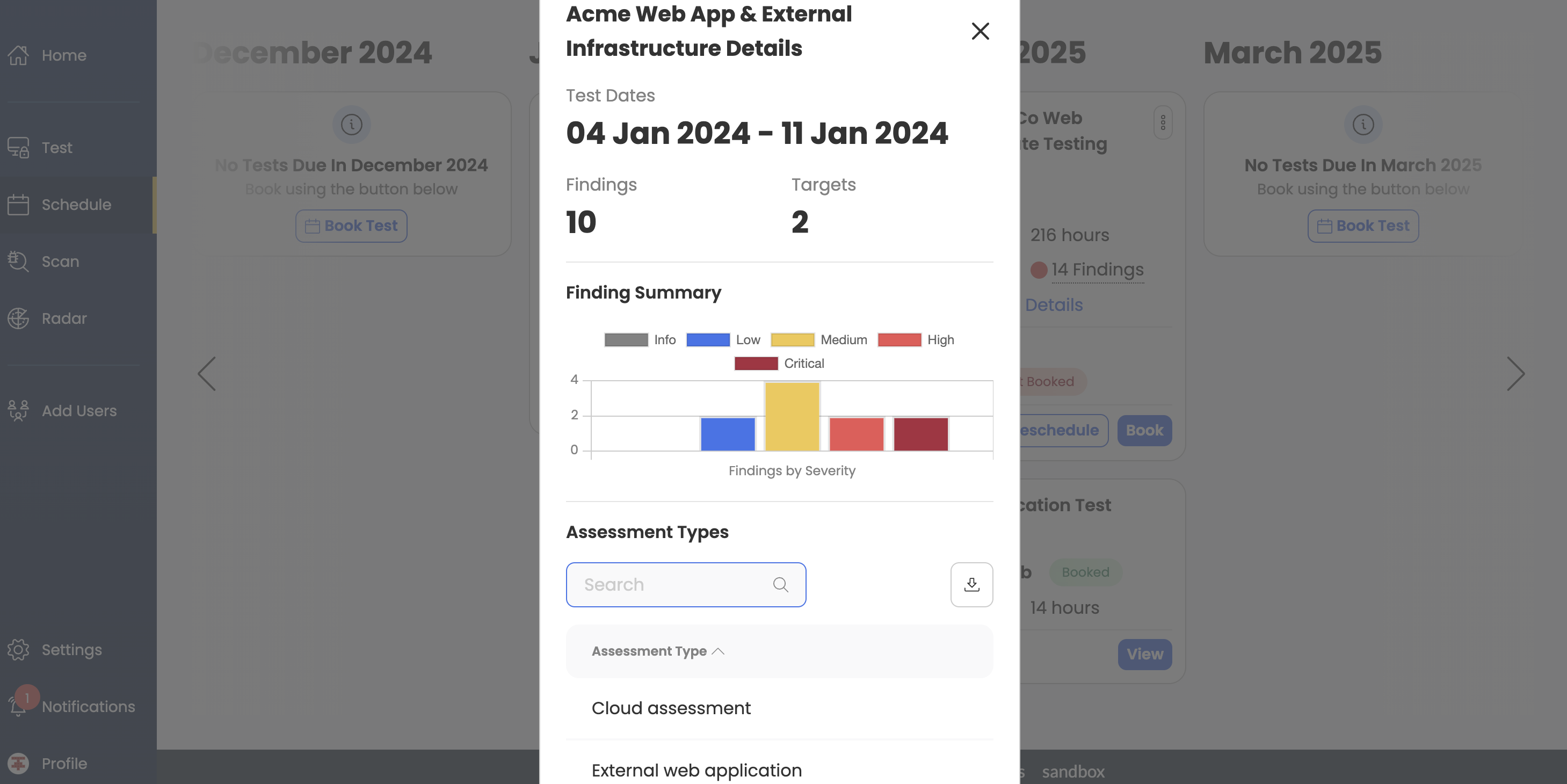
How long does an external pen test take?
The duration of a test depends on the size and functionality of your target. We ask two straightforward scoping questions to assess the complexity of your environment, which helps us estimate the time required for testing.
How often should you conduct an external infrastructure pentest?
A pentest should be conducted at least once a year, with additional tests carried out more frequently following any major changes, upgrades or software patches.
When will I receive my pentest report?
Our testers provide updates as they conduct their tests, so you receive notifications that can be integrated through your workflow apps when issues are discovered, rather than waiting until the entire test is complete and a report is generated.
Will my external network be disrupted during the test?
There should be no disruption as our penetration tests are performed carefully and systematically by experienced professionals. We offer the option to conduct tests in UAT, staging, or development environments to minimise any disruption to your operations. Throughout the process, we keep you informed, allowing you to promptly address any security issues as they arise.
What will we find in a network penetration test?
The goal of a network penetration test is to identify vulnerabilities before cybercriminals can exploit them. Common issues that may be found include missing patches, poorly configured firewalls, software, and operating systems. Understanding these weaknesses enables you to strengthen your security measures and better protect your network from potential threats.
What is the difference between web app testing and network penetration testing?
Web app pen testing finds vulnerabilities within a specific web app, such as issues with input validation, authentication, or security misconfigurations. External network pentesting, however, assesses an organisation's external-facing infrastructure, including servers, firewalls, and network devices. It looks for vulnerabilities like open ports, outdated software, and weak firewall settings that could allow unauthorised access to the internal network.
Is external infrastructure testing right for your business?
If your business relies on internet-facing systems, external infrastructure penetration testing is crucial for identifying and mitigating risks before they can be exploited by attackers. This testing is essential for any organisation looking to safeguard its network, protect sensitive data, and maintain a robust security posture.
