Threat intelligence involves gathering, analysing, and applying information about potential or current cyber attacks that could threaten an organisation's security. It provides insights into threat actors, their tactics, techniques, and procedures (TTPs), as well as indicators of compromise (IOCs). The ultimate goal of threat intelligence is to equip organisations with the knowledge to proactively defend against and respond to cybersecurity threats.
Hacker-powered Threat Intelligence
80% of breaches are caused by hackers finding and exploiting known vulnerabilities. Radar gives you the power to find these vulnerabilities before the bad guys do.
What is Threat Intelligence & why do we need it?
Breached Credentials
There are hundereds of data breaches every year containing leaked credentials. Attackers use these to gain access to sensitive accounts at scale.
Password Reuse
Gain insight into whether your users are reusing passwords across multiple sites. Reused breached credentials present additional risk.
Domain Fraud
Identify registered typosquat domains which may be attempting to impersonate your brand, as well as subdomain takeovers that would allow attackers to manipulate user's trust in your branding.
Sub Resource Integrity
Continuous monitoring of your application sub-resource integrity, to ensure your users don't inadvertently run malicious code like Magecart.
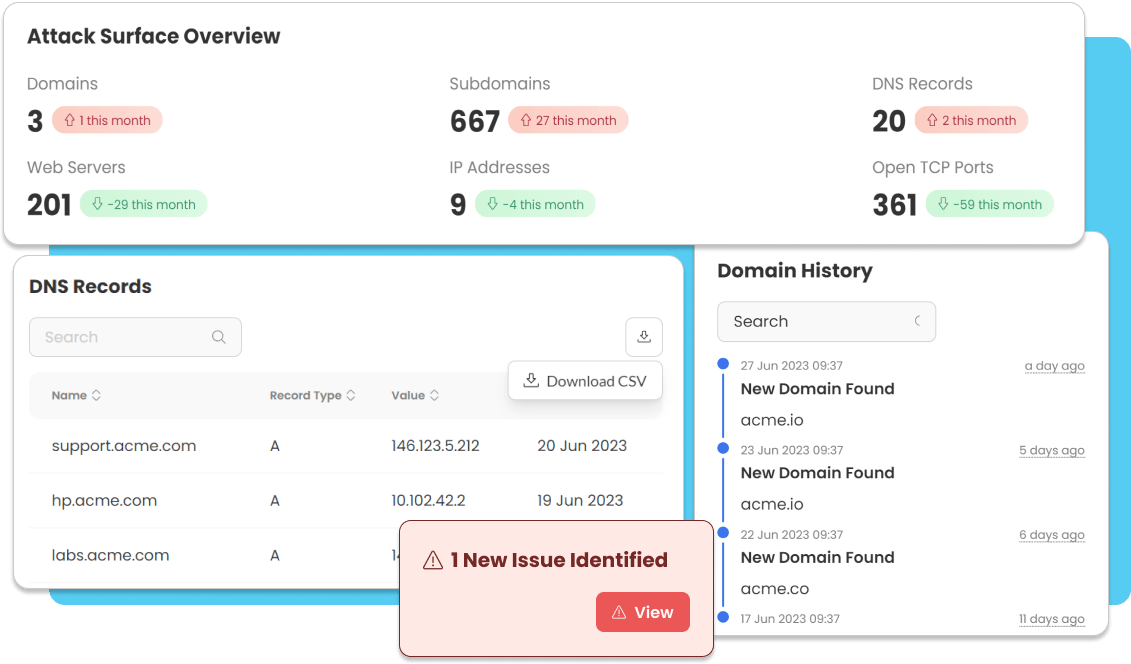
Attack surface monitoring
Get alerted when new services are exposed on your attack surface.
Certificate Monitoring
Get alerted for newly issued TLS certificates that belong to your company, or configure your own match rules to detect potential attacks. Manage Shadow IT and detect phishing attacks impersonating you, or your supply chain partners in the planning stage.
See Radar in Action
Watch how Radar can detect a phishing attack before the attack even takes place.
Detect
Radar identifies a newly issued certificate for a domain containing your companies name (or one of your chosen keywords) by monitoring certificate transparency logs. This means a new website has been setup which is using your companies name within its URL.
Report
Radar notifies you in real-time about the newly issued certificate. Using the information provided by Radar, you can make the decision as to whether the domain the certificate was issued for is hosting malicious content. Get instant alerts with our Slack and Teams integrations.
Prevent
If you deem that the domain is hosting content that is a potential risk, Radar will tell you all you need to know to block the planned attack. A targeted attack has been thwarted, and Radar gets back to work.
Frequently Asked Questions
Got a question you need answering? Hopefully our FAQs should help guide you
What is Radar and why is it useful?
Radar, our threat and attack intelligence tool, gathers info from across the Internet and dark web to scope out how exposed your organisation is to a potential attack.
Do I need a security team to use Radar?
No! Radar is designed to be user friendly and requires very little technical knowledge. Each module has a handy help guide explaining what the findings are and what they mean for your security.
What kind of things does Radar search for?
Radar searches for your Attack Exposure - any information available on your organisation for attackers to see, and your Attack Resistance - simple web based security controls that dramatically impact your risk.
Where does Radar look for information related to my organisation?
Attack Exposure modules search Radar’s own data stores and third party content on the internet and dark web - like breached credential dumps and Typosquat domains where attackers can register domains for phishing campaigns.
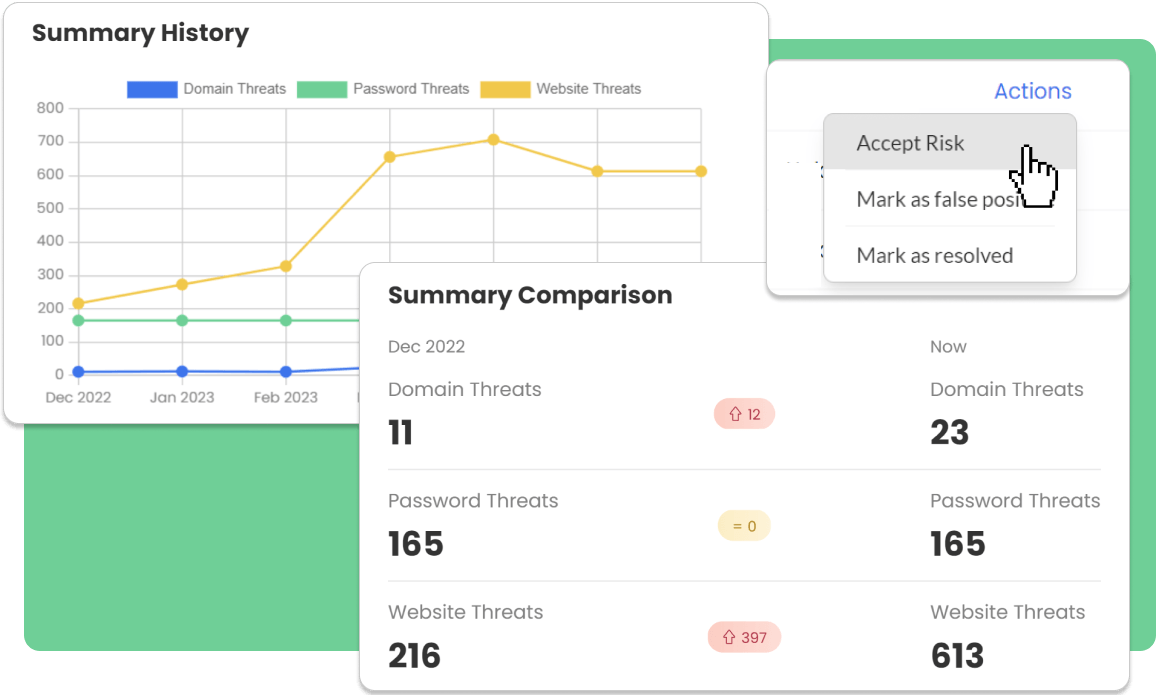
Can I track my security posture over time?
Yes! Radar is constantly scanning, and the OnSecurity Portal dashboard allows you to track your findings over time, so you can be alerted to an increase in suspicious activity.
Can Radar help me avoid a breach?
Yes! You can fix any issues found in the Attack Resistance modules to sure-up your web security. Although you can’t do anything about breached credentials, immediately changing passwords can mean any risk is contained.
How do I get notified of findings?
Radar will let you know as soon as it finds an issue - The OnSecurity Portal can notify you in-portal, via SMS, or through Slack, thanks to our integration features.
Do you search for missing security controls?
Yes. Radar’s Attack Resistance module monitors you against common web application security controls like SRI Hashes, Security Header Configurations and SSL certificates, enabling you to take immediate action.
How often does Radar check for information related to my organisation?
Radar checks either each month, each week or continuously, depending on which of our tiers you're subscribed to.
Do I need to have an enterprise-sized budget to use Radar?
No! We built Radar to give you enterprise-grade situational awareness, without the hefty price tag! Monitor your domain all year round with an affordable monthly subscription. See our pricing page for additional details.