The latest vulnerability scanning technology, used on every scan.
Efficient vulnerability management 24/7, with Scan
Remove the guesswork in detecting vulnerabilities in your internet-facing infrastructure.
Find and fix vulnerabilities before an attacker does
Cutting-edge Tech
Reduce Risk
Scan runs daily on our real-time tier, drastically reducing the window of opportunity for cyber-criminals.
Effortless Compliance
Instantly show evidence of scanning to comply with SOC II Type II, PCI-DSS, ISO27001 standards.
Integrate in your workflows
Slack, Teams, JIRA, ServiceNow integration, plus a fully-featured API.
Attack surface monitoring
Get alerted in real time when your attack surface changes, so you can take action before hackers do.
Easy setup
Automatic target detection lets you start scanning within seconds.
Find and fix vulnerabilities before an attacker does
60% of breaches are linked to poor patch management. Cyber-attackers constantly mass-scan the internet for known vulnerabilities that can be used to compromise organisations. Scan helps you detect and remediate vulnerabilities in your infrastructure rapidly, checking against over 20,000 common entry routes and drastically reducing opportunity for attack.
See Scan in Action
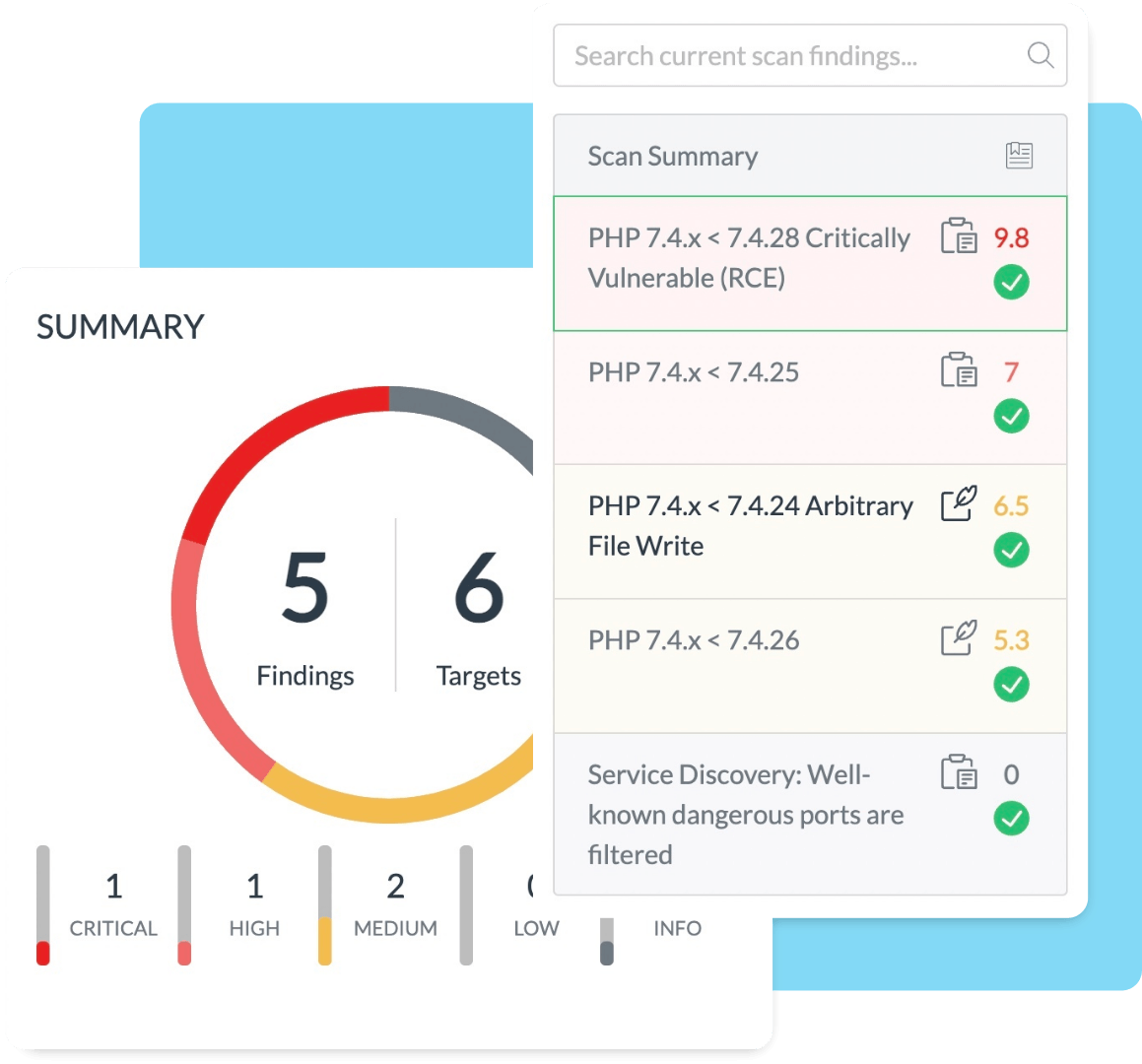
Scan alerts you to vulnerabilities in real time, so you can stay one step ahead of hackers.
Cutting edge scanning tech
Find the most dangerous vulnerabilities before the bad guys do with our cutting-edge vulnerability scanning technology. To get started, simply add the targets you want to protect, or better yet let us detect your targets with our OSINT technology.
Round-the-clock protection
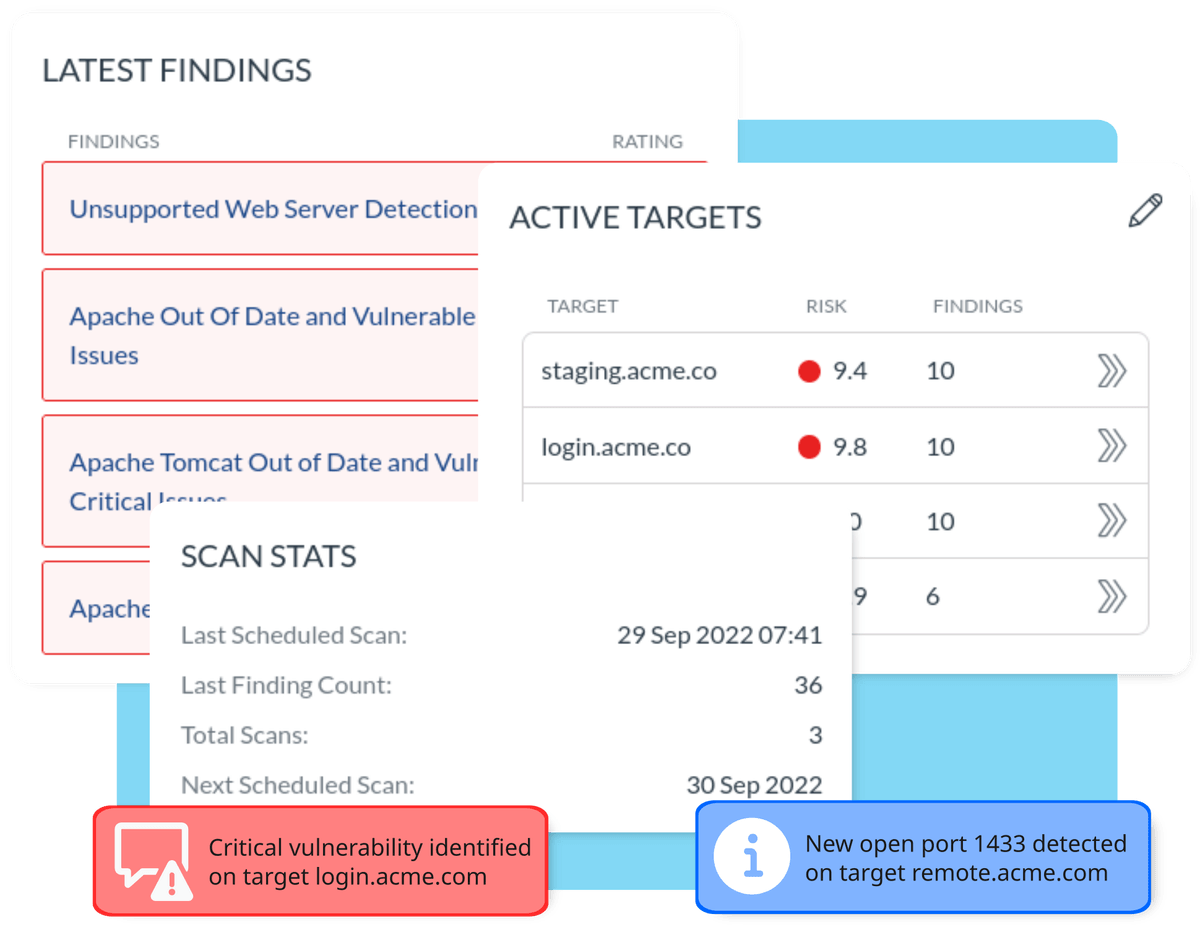
Scan gets to work, identifying and detecting vulnerabilities in your targets. It works 24/7 on our real-time tier, and will let you know as soon as a new vulnerability arises. Our actionable findings tell you what the problem is, where we found it and what you need to do to take action immediately to fix the problem and stay safe.
Attack surface monitoring
Continuous, real-time attack surface monitoring. Scan will notify you as soon as a new port or service opens on your Internet-facing perimeter, so you can stay in the know and keep your business safe.
Frequently Asked Questions
Got a question you need answering? Hopefully our FAQs should help guide you
What are the advantages of using a vulnerability scanner?
60% of breaches are linked to a vulnerability where a patch was available, but not yet applied - and regular vulnerability scans check your systems for missing patches and misconfigurations, reducing your risk window.
How does Scan work?
Scan carries out over 40,000 checks for missing patches, security misconfigurations, default passwords, dangerous services or otherwise potentially harmful security vulnerabilities in your configured targets.
Which parts of my infrastructure do you scan?
Scan monitors your external (internet facing) assets - This includes web applications and web servers. If you don’t know what your assets include, we can identify them for you using OSINT (Open Source Intelligence) gathering.
How does scanning for vulnerabilities help me avoid being targeted by cybercriminals?
Bad actors are constantly mass-scanning the Internet for vulnerabilities, using their own scanning tools. Scanning your internet facing assets regularly helps you identify and fix your vulnerabilities before an attacker has a chance to exploit them.
How does an attacker choose their target?
Most people think attackers choose their targets first, but often it’s easy for an attacker to use a scanning tool and a known vulnerability to see which organisations they should exploit.
How important is frequent scanning?
With bad actors scanning continuously, it’s important to keep the window of risk as small as possible. If you only scan every 90 days, but an attacker can get to work in minutes, you’re leaving your organisation vulnerable!
How does vulnerability scanning help my cyber posture?
Vulnerability scanning helps not only to identify areas you can improve, but also provides an inventory of your assets. Plus, the OnSecurity Portal dashboard rates each vulnerability with a CVSS score, helping you to prioritise and understand your risk.
How quickly will I get my results?
Immediately! The OnSecurity Portal will notify you as soon as a finding is discovered, in-portal, via SMS, or Slack, thanks to our integration features.
Can I use my Scan report for compliance purposes?
Yes! In fact, many compliance certifications, such as PCI DSS, or the NHS DPS will specifically require you to submit a vulnerability scan report. You can download a report directly from the OnSecurity Portal dashboard.