Web application penetration testing Services
With OnSecurity, you can ensure your web applications are secure, maintain customer trust, and comply with industry regulations, all while minimising risk to your business.
What is web application penetration testing?
Web application penetration testing is a simulated security assessment designed to uncover weaknesses in a business’s web applications. Penetration testing helps identify vulnerabilities that could enable attackers to:
- Gain access to user accounts
- Compromise application data
- Cause reputational damage
- Disrupt web application functionality
Our CREST-accredited testers use a combination of manual techniques and automated tools to thoroughly assess application security, pinpointing vulnerabilities that real-world attackers actively exploit. Web application penetration testers leverage deep expertise in app development to identify and address common risks such as:
- Injection flaws allowing unauthorised access
- Authentication weaknesses enabling account takeovers
- Broken access controls granting improper permissions
- Security misconfigurations leaving entry points open
- Database interaction errors exposing sensitive data
- Input validation problems enabling injection attacks
- Flaws in the application logic that can be exploited
Comprehensive penetration testing is crucial to uncover these vulnerabilities before they are discovered and exploited by malicious actors. Our experienced testers methodically assess the security posture and recommend remediation measures to keep your web applications secure.
Why do you need a web application pentest?
Web applications are a top target for hackers seeking to steal data, disrupt services, or damage your brand. With cyber threats growing more frequent and sophisticated, a web application pentest is crucial. It simulates real-world attacks to find and fix vulnerabilities before they can be exploited, helping you avoid costly breaches and downtime.
Beyond just protection, it demonstrates a commitment to security, builds customer confidence, and ensures compliance with industry regulations. Investing in regular pentests is the smartest way to defend your business, reputation, and bottom line from the ever-present risk of cybercrime.
Secure Your Web App. Start a Penetration Test Today!
Identify injection flaws, broken authentication, and misconfigurations before attackers do. Our manual-first, CREST-accredited testing delivers deep insights and actionable fixes
Crest-accredited web application pentesting
Why trust OnSecurity with your web application pentesting? Because we’re CREST-approved, adhering to the highest industry standards. Our CREST certification isn’t just a badge—it’s your assurance of top-tier security:
- Our methodologies, processes, and procedures undergo rigorous external vetting.
- Our pentesters are CREST-certified, having demonstrated their expertise through stringent assessments.
- We employ a best-in-class, manual-first approach to uncover vulnerabilities that others might miss.
Choose OnSecurity for unmatched excellence and thorough protection for your web applications.

Web application penetration testing with OnSecurity
With OnSecurity, you can ensure your web applications are secure, maintain customer trust, and comply with industry regulations, all while minimising risk to your business.
Quick, high-quality pentests
Discover why our user-friendly platform and AI + human approach make pentesting hassle- free.
Flexible subscription plans
Simplify your testing and monitoring with a single monthly payment, combining regular penetration tests and continuous vulnerability scanning. Get predictable costs while receiving ongoing protection.
Instant quote & customised plans
Receive a real-time, personalised cost estimate through our intuitive platform. Tailor your testing needs with configurable options that suit your business goals and security requirements.
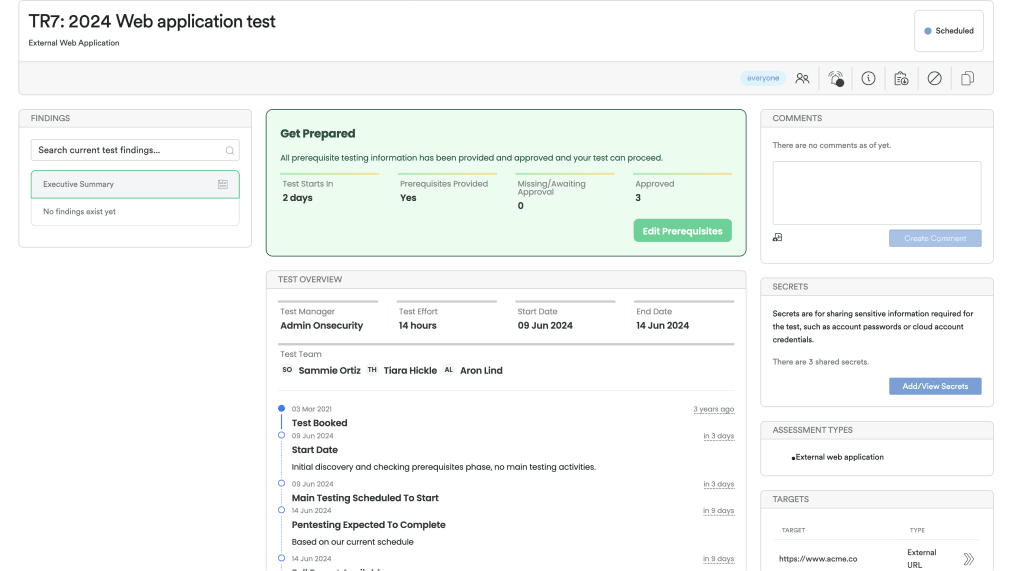
Effortless platform access
No more long scoping processes. Book tests directly through our platform or get personalised assistance from our sales team. Enjoy streamlined communication and automated workflow notifications for maximum efficiency.
Immediate, actionable reports
Access your findings instantly through our platform. Generate detailed reports at any time, offering both technical insights and high-level summaries—without the wait.
Free retests for resolved issues
Once you’ve addressed vulnerabilities, we’ll retest them for free within a flexible window, ensuring your systems remain secure at no additional cost.
Ongoing protection & threat intelligence
Sign up for continuous monitoring to access automated vulnerability scanning, along with situational awareness through threat intelligence, ensuring your defences stay up to date year-round.
Other Types of penetration testing
Find the penetration test to best suit your business and cybersecurity needs.
Frequently Asked Questions
Got a question you need answering? Our FAQs should help guide you
A pentest should be conducted at least once a year, with additional tests carried out more frequently following any major changes, upgrades or software patches.
At OnSecurity, we’re CREST-approved, meaning our testing methods meet the highest industry standards. Most of our testers are CREST certified, proving their advanced skills in finding vulnerabilities. This external validation means that our manual-first approach delivers thorough, reliable pentesting, giving you confidence in our expertise.
Our testers provide real-time updates as they conduct their tests, so you receive immediate notifications when issues are discovered, rather than waiting until the entire test is complete and a report is generated.
The duration of a test depends on the size and functionality of your target. We ask two straightforward scoping questions to assess the complexity of your environment, which helps us estimate the time required for testing.
Our tests are conducted safely and systematically by skilled professionals, allowing you to continue your work without interruption. We’re also happy to work in UAT, staging or development environments if our clients prefer. We provide real-time updates on any security issues we discover, enabling you to address them promptly before they can be exploited by criminals.
At OnSecurity, our testing team identifies a wide range of vulnerabilities, including common ones like SQL injection, cross-site scripting, and cross-site request forgery. We also examine business logic and permissions issues, using our expertise to spot flaws that could emerge from unexpected use. By applying recognised attack classifications such as OWASP, CWE, and MITRE CAPEC, we address all vulnerabilities, including minor ones that could be combined to create serious risks.
Web application penetration testing identifies security vulnerabilities within applications, whereas network penetration testing—also known as infrastructure penetration testing—focuses on discovering cybersecurity weaknesses that could jeopardise on-premises and cloud environments. Unlike web app testing, which examines the application’s environment and setup, network pen testing assesses potential vulnerabilities both inside and outside an organisation’s network perimeter.
Conducting web application penetration testing can be highly beneficial for your business, whether you develop proprietary applications in-house or use apps provided by third-party vendors. It helps to reduce the financial and reputational damage that could occur if a security vulnerability is discovered after your application has been launched or shared with customers. While web application pen testing offers many advantages, your business may also benefit from other types of security assessments depending on your specific requirements, such as mobile application security testing or cloud penetration testing.