Discover and highlight weaknesses in your cloud security infrastructure with our CREST-accredited cloud penetration testing service.
Cloud penetration testing
Cloud penetration testing with OnSecurity
Our team of experts can provide your business with a fast, flexible cloud penetration testing service that allows you to secure your cloud environment and meet compliance requirements. We can assess your cloud estate and replicate what real-life hackers do, but in a legal framework to identify any weaknesses.

Test all major cloud providers
We test all major cloud providers including: Amazon Web Services (AWS) penetration testing, Microsoft Azure penetration testing and Google Cloud Platform (GCP) penetration testing.
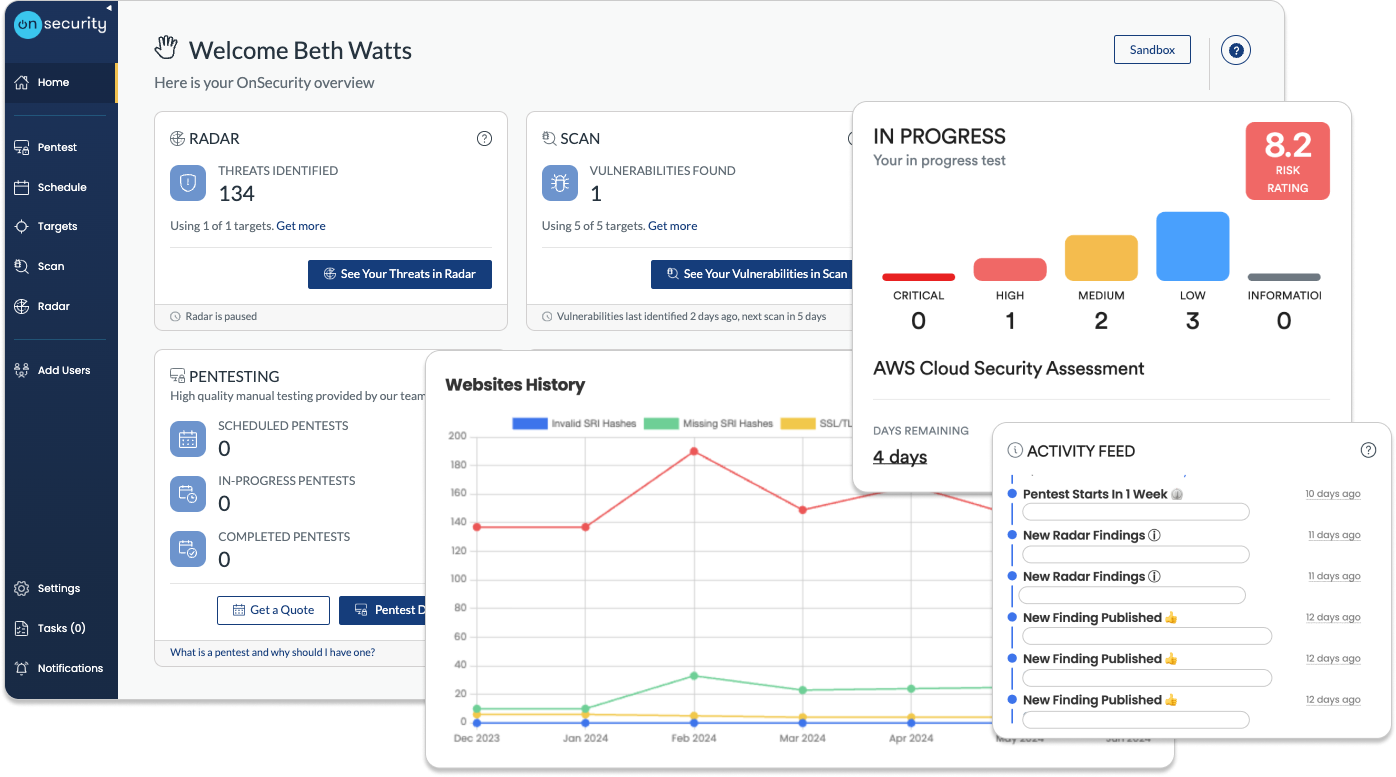
Instant online booking
When booking instantly, you'll be able to meet urgent compliance and client demands, See & remediate findings in as little as 8 minutes and start fixing critical issues immediately.
User-friendly platform
You'll pay only for the hours you need with flexible free retesting, ensure there are no hidden fees or minimum charges and have intuitive help guides to navigate the platform.
Get an Instant Cloud Security Pentest Quote
Want to know how much a cloud security pentest would cost? Try out our instant quote generator to get started.

What is cloud penetration testing?
Cloud penetration testing is a cyber security method used to review how secure your cloud-based systems, applications and infrastructure are from potential threats. The main goal of cloud penetration testing is to protect your data and stop any potential hackers early, before they cause damage. It checks if hackers can break into your cloud systems and steal sensitive data.
Our cloud penetration testing service uses ethical hacking to test your cloud exposure, and a white box authenticated audit to test against your cloud services.
Why do you need a cloud pentest?
Put simply - your business is at risk without it. Cloud misconfigurations are easy to miss but devastating when exploited. Traditional security measures often fall short in cloud environments, and compliance requirements are constantly evolving. Meanwhile, cyber threats are becoming more sophisticated daily, specifically targeting cloud vulnerabilities.
Your data is your lifeline. One breach could cost millions and destroy customer trust. That's where our CREST-accredited cloud penetration testing comes in. We:
- Identify vulnerabilities before hackers do
- Simulate real-world attacks on your systems
- Ensure you meet industry standards and compliance requirements
Our testing provides a clear roadmap to strengthen your defences, going beyond basic security measures to truly safeguard your cloud environment. Don't leave your cloud security to chance. Invest in expert testing to protect your business, data, and reputation.


Crest-accredited cloud pentesting
Why trust OnSecurity with your cloud penetration testing? Because we're CREST-accredited, meaning we're held to the highest industry standards. Our CREST certification isn't just a badge - it's your guarantee of excellence:
- All our methodologies, processes, and procedures are externally vetted.
- Our pentesters are CREST-accredited, having proven their skills through rigorous testing.
- We use a best-in-class, manual-first approach to find vulnerabilities others might miss.
Cloud security challenges
Cloud security presents critical challenges for businesses like yours. These challenges are daunting, but they can be overcome. Proper cloud security testing and expertise can help your organisation navigate these risks confidently.
Data breaches
These pose a severe threat, often resulting in substantial fines and significant reputational damage. The impact on an organisation can be devastating.
Compliance requirements
Regulations such as GDPR, PCI DSS, and HIPAA mandate strong cloud security postures. Understanding responsibilities is crucial.
Lack of expertise
With enterprises typically managing 3-4 cloud environments of varying complexity, many organisations struggle to secure their cloud presence effectively.
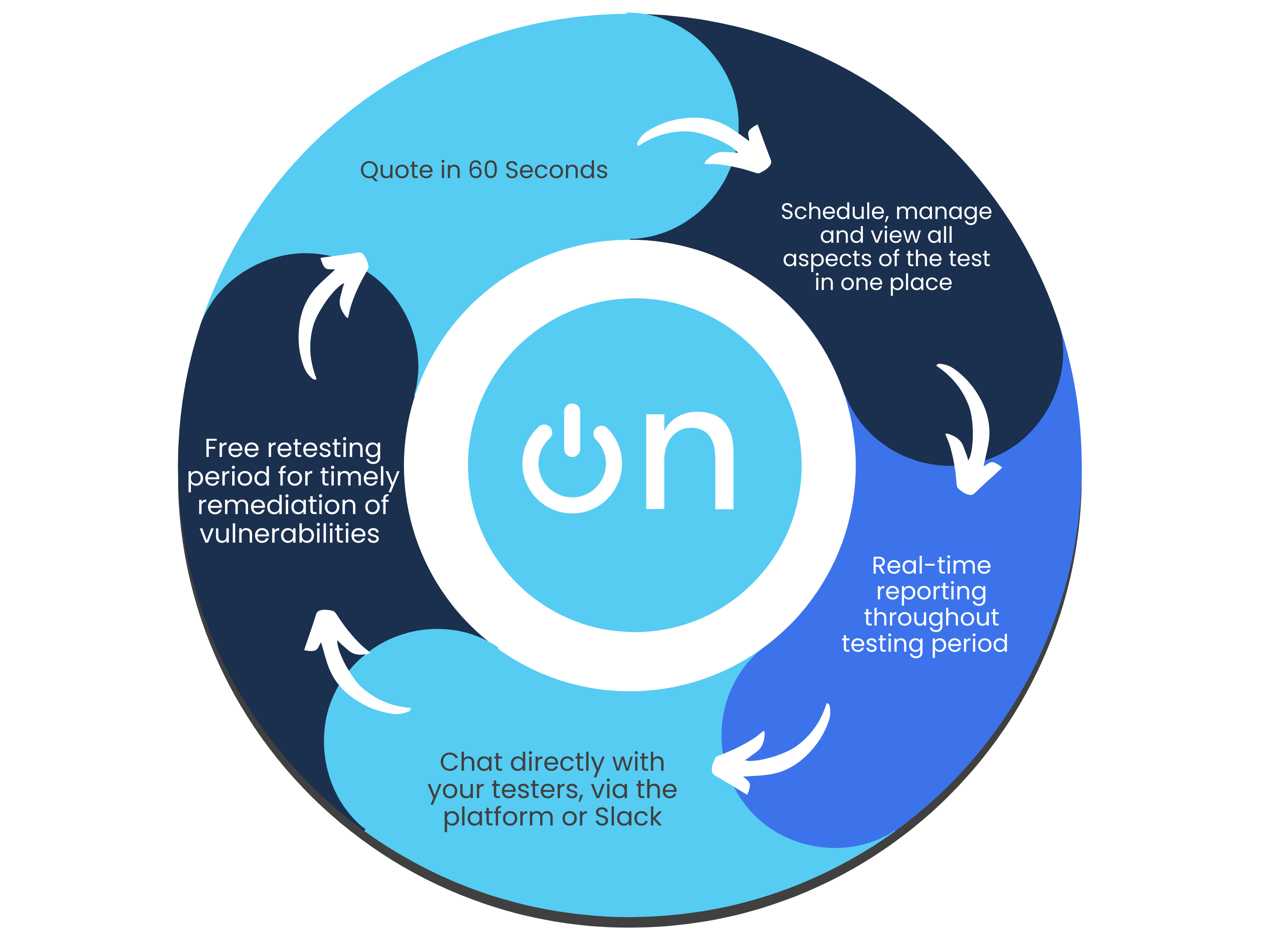
Quick, high-quality pentests
Discover why our user-friendly platform and AI + human approach make pentesting hassle- free.
Flexible subscription plans
Simplify your testing and monitoring with a single monthly payment, combining regular penetration tests and continuous vulnerability scanning. Get predictable costs while receiving ongoing protection.Instant quote & customised plans
Receive a real-time, personalised cost estimate through our intuitive platform. Tailor your testing needs with configurable options that suit your business goals and security requirements.Effortless platform access
No more long scoping processes. Book tests directly through our platform or get personalised assistance from our sales team. Enjoy streamlined communication and automated workflow notifications for maximum efficiency.Continuous, real-time testing
Stay informed with real-time progress notifications and direct communication with testers via in-platform comments. Benefit from ongoing vulnerability assessments to proactively detect and address risks.Immediate, actionable reports
Access your findings instantly through our platform. Generate detailed reports at any time, offering both technical insights and high-level summaries—without the wait.Free retests for resolved issues
Once you’ve addressed vulnerabilities, we’ll retest them for free within a flexible window, ensuring your systems remain secure at no additional cost.Ongoing protection & threat intelligence
Sign up for continuous monitoring to access automated vulnerability scanning, along with situational awareness through threat intelligence, ensuring your defences stay up to date year-round.
Other types of penetration testing
Find the penetration test to best suit your business and cybersecurity needs.
Frequently Asked Questions
How often should you test your cloud platform?
A pentest should be undertaken at least once a year, with additional tests performed after any major changes, upgrades or software patches.
Do I need permission from my cloud provider?
Yes, you typically need permission from your cloud provider before conducting a penetration test. Most cloud providers, such as AWS, Azure, and Google Cloud, require you to submit a formal request outlining the scope and nature of the test to ensure it complies with their policies and does not disrupt their services or other customers.
What type of cloud pentest do you need?
The type of cloud penetration test you need depends on your cloud deployment model and specific security concerns. Common types include infrastructure testing (focusing on the security of cloud servers, storage, and network components), application testing (assessing the security of applications running in the cloud), and configuration reviews (ensuring your cloud environment is set up according to best practices). The scope may also vary based on whether you are testing public, private, or hybrid cloud environments.
When will I receive my report?
Our testers report in real time as they test, so you can get notified immediately when something is found, instead of having to wait until the test is complete and a report written up.
Is OnSecurity a CREST-accredited provider?
Yes. OnSecurity is CREST-approved, and all our testers are qualified CREST testers.
How long does a cloud pentest take?
How long a test will take will depend on the size of your target and its function. We ask 2 simple scoping questions to gauge the complexity of your environment which then informs the time we think it will take to test.
Will work be disrupted during the test?
Our tests are carried out in a safe and controlled manner by experienced testers, so you can continue with work as normal. We tell you about the security issues we find in real-time, so you can fix them before criminals have a chance to exploit them.
