Phishing scams often serve as the initial breach point for many security incidents. Our phishing testing services simulate these deceptive attacks to identify vulnerabilities in your email security. By revealing weaknesses, we help you strengthen your defences and prevent these attacks from compromising your business.
Phishing testing services
Phishing testing services with OnSecurity
Phishing testing goes beyond standard checks to provide expert insights into vulnerabilities in your email security. By simulating phishing attacks, we reveal critical weaknesses that could be exploited by scammers, helping you strengthen your defences
Identify phishing vulnerabilities
Spot weaknesses in how well your team detects and handles phishing attempts, determine which employees are most susceptible to phishing scams and find gaps in your current security training and awareness efforts.
Reduce phishing scam risk
Lower the chances of successful phishing attacks that could expose sensitive data, prevent potential financial losses and data breaches from phishing and shield your business from the negative impact of security incidents.
Boost security awareness
Assess how effective your current cybersecurity training is in real scenarios, enhance training programmes with insights from simulated phishing attacks and provide your team with hands-on experience to improve their response to actual threats.
What is phishing testing?
Phishing scams are deceptive attempts to obtain sensitive information, such as credit card details, usernames, and passwords, by pretending to be a trusted source, usually through emails. Scammers trick individuals into revealing personal data, downloading malware, or taking other harmful actions for monetary gain.
A phishing test involves sending simulated phishing emails to staff across your organisation. These emails mimic real phishing attempts, prompting employees to click links, enter passwords, or perform other typical actions. The goal is to help staff recognise and learn from their mistakes in a controlled environment, without the severe consequences of an actual phishing attack.
Get a Instant Phishing Pentest Quote
Want to know how much a phishing pentest would cost? Try out our instant quote generator to get started.
Why do you need a phishing test?
Phishing attacks can bypass even the best cyber security measures by tricking your employees into revealing sensitive information or downloading malware. By simulating these attacks, you can pinpoint weaknesses in your email security and staff awareness. This proactive approach helps you address potential vulnerabilities before real scammers can exploit them, keeping your business better protected.


CREST-accredited phishing pentesting
At OnSecurity, we deliver trusted phishing penetration testing services, backed by our CREST (Council of Registered Ethical Security Testers) accreditation. This certification ensures our testing methods, processes, and procedures meet the highest industry standards.
- CREST-accredited: Our phishing testing is approved by CREST, guaranteeing adherence to rigorous industry benchmarks.
- Expert team: Most of our testers are CREST-certified, having completed extensive training to effectively identify and address phishing vulnerabilities.
- Hands-on approach: We use practical, hands-on methods to uncover weaknesses that automated tools might overlook.
With OnSecurity, you can trust that your phishing tests are conducted by skilled professionals using best-in-class techniques and maintaining top industry standards.
Phishing security challenges
Addressing phishing security threats requires a thorough understanding of the tactics used by attackers and the vulnerabilities they exploit:
Phishing vulnerabilities
Weaknesses in email security and staff awareness can be targeted by scammers to trick individuals into revealing sensitive information or downloading malware.
Varied attack methods
Phishers may use different approaches, such as deceptive emails, fraudulent links, or fake login pages, to manipulate individuals into disclosing credentials or clicking harmful attachments.
Evolving tactics
Phishing strategies and techniques are constantly evolving, making it essential to stay updated on the latest threats and regularly test your defences.
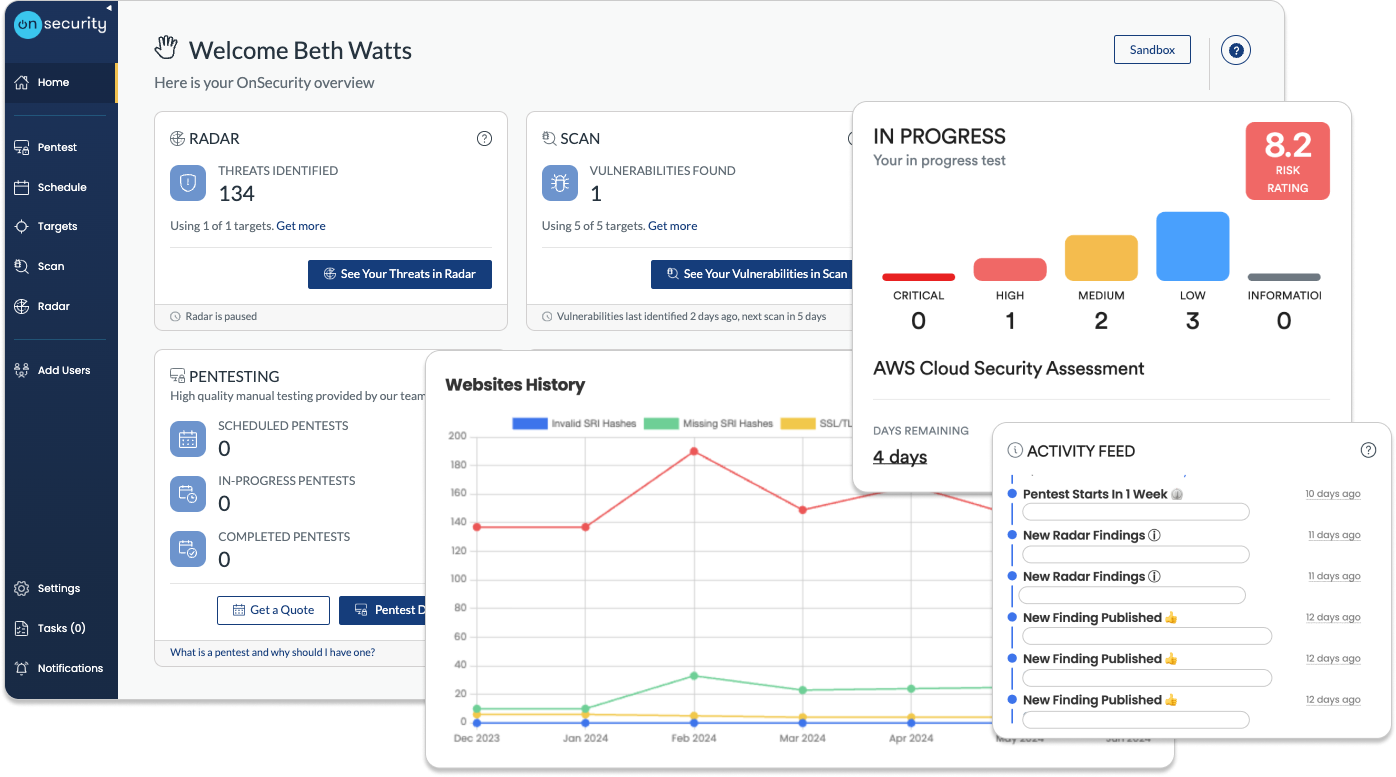
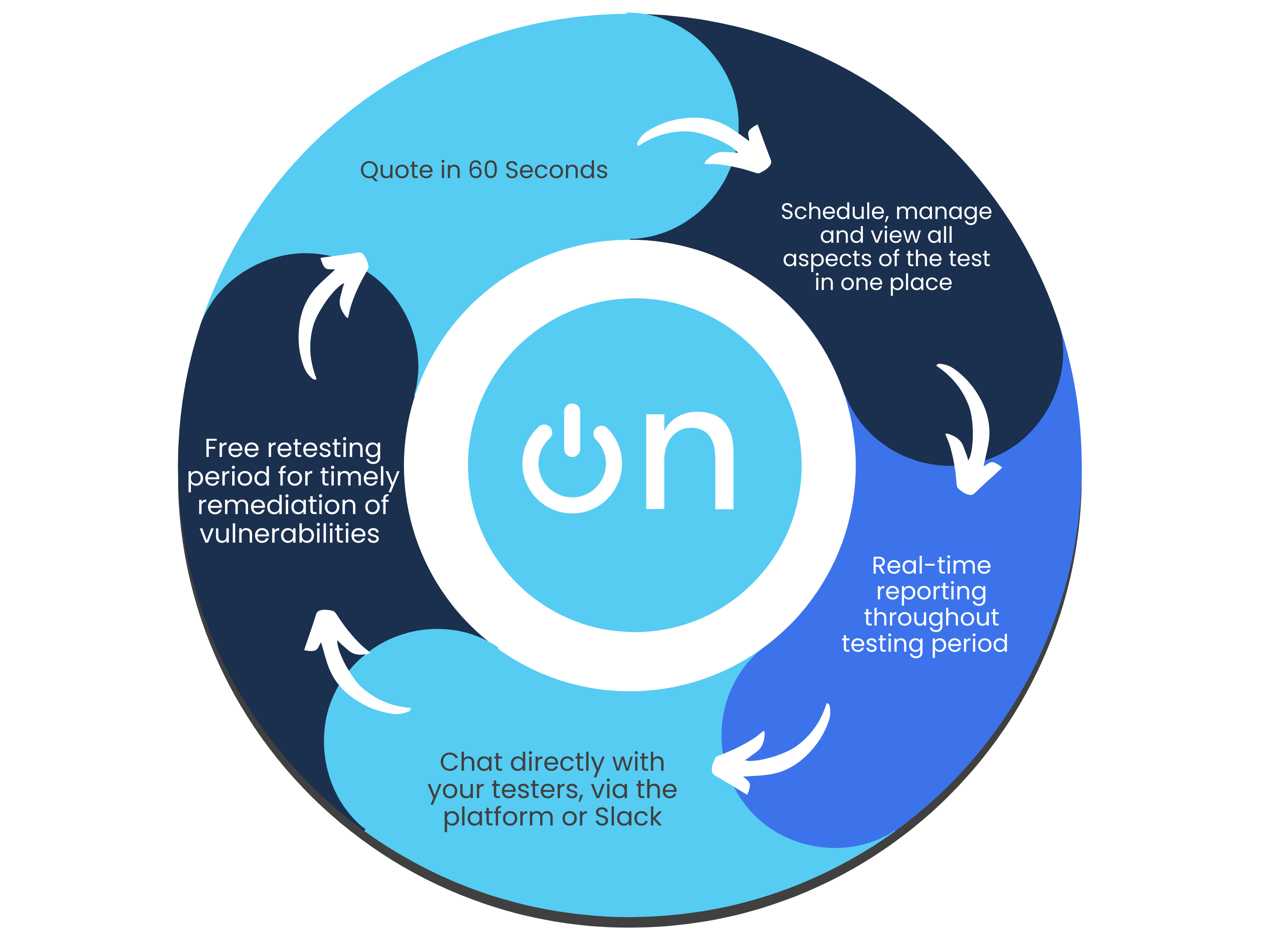
Quick, high-quality pentests
Discover why our user-friendly platform and AI + human approach make pentesting hassle- free.
Flexible subscription plans
Simplify your testing and monitoring with a single monthly payment, combining regular penetration tests and continuous vulnerability scanning. Get predictable costs while receiving ongoing protection.Instant quote & customised plans
Receive a real-time, personalised cost estimate through our intuitive platform. Tailor your testing needs with configurable options that suit your business goals and security requirements.Effortless platform access
No more long scoping processes. Book tests directly through our platform or get personalised assistance from our sales team. Enjoy streamlined communication and automated workflow notifications for maximum efficiency.Continuous, real-time testing
Stay informed with real-time progress notifications and direct communication with testers via in-platform comments. Benefit from ongoing vulnerability assessments to proactively detect and address risks.Immediate, actionable reports
Access your findings instantly through our platform. Generate detailed reports at any time, offering both technical insights and high-level summaries—without the wait.Free retests for resolved issues
Once you’ve addressed vulnerabilities, we’ll retest them for free within a flexible window, ensuring your systems remain secure at no additional cost.Ongoing protection & threat intelligence
Sign up for continuous monitoring to access automated vulnerability scanning, along with situational awareness through threat intelligence, ensuring your defences stay up to date year-round.
Other types of penetration testing
Find the penetration test to best suit your business and cybersecurity needs.
Frequently Asked Questions
What is penetration testing?
Pentesting, also known as penetration testing, is a critical security practice where a security professional adopts a hacker’s mindset to identify security issues in an organisations IT infrastructure. Penetration testing simulates real-world hacking activities, comprehensively evaluating your digital defences. By engaging in pentesting, businesses can uncover and remediate vulnerabilities before malicious hackers exploit them.
What’s the difference between manual and automated pentesting?
Automated pentesting and vulnerability scanning relies on software tools to quickly assess for known vulnerabilities. Manual pentesting uses experts to identify complex vulnerabilities, tests in real-time and uncovers subtle issues that automated tools might miss. We believe in manual-first testing, and investing in developing talent through a structured and rigorous training programme. That's how we keep the quality of our tests so high.
Do I need a penetration test?
A penetration test is the best way to know for sure if your organisation is an easy target for hackers. The test will show you both how strong your cyber defences are, but what the potential outcomes of a breach could be. It can also ensure compliance with security regulations and enhance customer trust through demonstrated security commitment.
Recent research reveals that the average breach now costs $4.35 million, with global cybercrime expenses projected to surge by 23% annually. By 2027, these costs could reach a staggering $23.84 trillion per year. This alarming trend underscores the critical need for robust cybersecurity measures.
Penetration testing is a vital cyber security solution. As cyber attacks grow more sophisticated and frequent, proactive testing of your defences becomes even more important. Safeguard against potential breaches and avoid devastating financial impacts. Implementing pentesting services is no longer optional – it’s a necessity for many businesses seeking to protect their assets and reputation.
What should I get pentested?
All types of computer systems, networks, applications, and devices that are used to store, process, or transmit sensitive data should be tested. This includes web applications, mobile applications, wireless networks, cloud-based systems, and IoT devices.
The scope of the penetration test should be determined by the organisation's risk assessment and compliance requirements. It's important to test all systems and applications that have access to valuable data to ensure that they are secure and protected against potential attacks.
How much does a pen test cost?
The cost of a penetration testing service can vary depending on the scope, duration, and complexity of the project. Generally, factors that can affect the cost of a penetration test include the number of systems to be tested, the depth and breadth of the testing, the type of testing required (e.g., web application, network, mobile), and the level of reporting and follow-up support needed.
Our transparent, hourly billing means that everybody pays the same rate, and we quote to the nearest hour, not the nearest day.
If you are interested in obtaining a quote for a penetration test, you can get an instant quote from our quote builder.
What's the difference between vulnerability scanning and pentesting?
A vulnerability scan is done using an automated tool to sweep your systems for known vulnerabilities. Penetration testing is a highly skilled, manual process in which a tester finds and attempts to exploit a vulnerability. Find out more about our efficient vulnerability management tool and start your 14 day free trial.
How many scoping questions do you ask? / How do you scope a pentest?
OnSecurity requires just two simple scoping questions to determine the scale of your test. We then use an algorithm to generate you an estimated quote in just a few clicks.
Are your pentests disruptive? Can I continue working while the test is being done?
Our tests are carried out in a safe and controlled manner by experienced testers, so you can continue with work as normal. We tell you about the security issues we find in real-time, so you can fix them before criminals have a chance to exploit them.
Can I speak to my tester directly?
Yes! You can chat directly to your tester in-platform or via Slack during the test.
How can I be sure my test is cost effective?
OnSecurity works in hours, not days, so you get a quote based on the actual time your test will take, without any padding or rounding up to the nearest day. Plus, we report as we go - so no waiting around while a tester spends days writing up a report before you can action any findings.
When will I be notified of findings?
Our testers report in real time as they test, so you can get notified immediately when something is found, instead of having to wait until the test is complete and a report written up.
Do you offer free retesting?
Yes! OnSecurity will retest any findings you've fixed for free, just book them in directly through our platform within 7 days of the test completion date.
How long does a pentest take?
How long a test will take will depend on the size of your target and its function. We ask 2 simple scoping questions to gauge the complexity of your environment which then informs the time we think it will take to test.
What if I need to cancel or reschedule a test?
No problem! We know that things don't always go to plan, so we don't charge you any fees to cancel or reschedule a test.
