The US National Institute of Standards and Technology (NIST) assists organisations in enhancing their security strategies and mitigating cyber risks.
The NIST cybersecurity framework helps businesses protect against cyber risks by providing guidance on security measures.
It helps businesses understand the cyber threat, and assess and determine whether the organisation has gaps in their security infrastructure. It supports security teams to improve cybersecurity risk management and enables effective communication with internal and external stakeholders to ensure the business is presenting a concise risk management process.
The structure consists of three components: the Core of the Framework, the Implementation Tiers of the Framework, and the Profiles of the Framework.
Let’s look into these components a little further…
What is the Framework Core?
This element comprises a collection of cybersecurity tasks, results, and relevant references that are universally applicable across vital infrastructure sectors.
The Core outlines a set of gold standard guidelines and practices for executive teams right through to the operations teams to follow in regard to cybersecurity activities. Consisting of five functions - identity, protect, detect, respond, and recover - the Framework Core provides a high-level, strategic view of the business continuity towards potential risks.
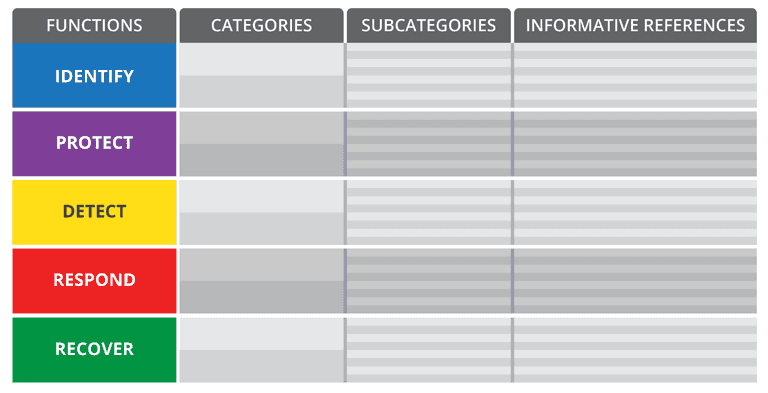
Using the framework above, businesses can outline their risk management strategies by organising the cybersecurity risk into categories and subcategories, enabling a straightforward approach to address and overcome threats as well as the actions required to improve the security infrastructure.
Reverting to the five functions in the Framework Core, these should be used to form a concurrent strategy that addresses dynamic cybersecurity risk. These functions are defined below:
Identity -
Managing and understanding cybersecurity risk associated with systems, people, assets, data and capabilities.
Protect -
Take steps to prevent or control the impact of a cyber-attack. Make sure that essential services can still be maintained.
Detect -
Identify and analyse possible cyber attacks before they take place. With a timely discovery, businesses can put measures in place to prevent the attack. Which leads up nicely to respond.
Respond -
Have the appropriate measures in place to act and respond to a cyber breach.
Recover-
To maintain resilience, develop strategies to overcome any implications caused by a cybersecurity incident. Restore functions and assets that were impacted by an attack.
Framework Implementation Tiers
This component of the NIST cybersecurity framework provides context on how an organisation has scoped risk and the activities in place to overcome and manage that risk. A clue is in the name, this element focuses on different tiers that identify the level of risk that the business is in. Ranging from partial (tier 1), risk-informed (tier 2), repeatable (tier 3) to adaptive (tier 4).
Framework Profiles
Combining all elements of the NIST cybersecurity framework, the ‘profile’ is made up of the functions, categories and subcategories that form the cybersecurity strategy. The profile establishes a roadmap for reducing risk aligned with the business’s overarching goals and considers industry best practices.
Framework profiles describe the present condition or future state of specific cyber activities. For example, the ‘Current Profile’ would state the active cybersecurity measures. Whereas the ‘Target Profile’ would identify the measures needed to overcome the desired security strategy.
Using the Framework
Depending on the complexity of each business, the NIST framework can be interpreted in different ways. Once a business has completed the framework steps, it shall enable them to understand, manage and prioritise cybersecurity risks. The framework will support the business in making informed decisions about its cybersecurity approach and the actions it wants to take.
Combining all three parts of the NIST cyber security framework, businesses can leverage a cybersecurity strategy that combats threats and ensures adequate measures are set in place to prevent reputational and financial damage.
Looking to improve your business’s cyber security strategy? Start today